This blog is a continuation of the “Part 1 – Technical configuration for SAP SuccessFactors to Azure Active Directory user provisioning“.
In section, we will focus on the Technical configuration for SuccessFactors Writeback.
Note:
For this demonstration, I have already created an Azure AD tenant and using SAP SuccessFactors & Azure trail account for the POC.
We can use the same API user(SFAPI2) which we created in part1(step 1 to 4) .
Steps need to perform in SAP SuccessFactors
Step 1: SuccessFactors Writeback provisioning app uses certain code values to identify email in Employee Central.
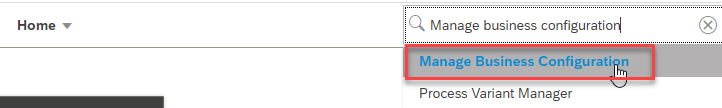
1.1 In SuccessFactors Admin Center, search for Manage business configuration.
1.2 Under HRIS Elements, select emailInfo and click on the Details for the email-type field.
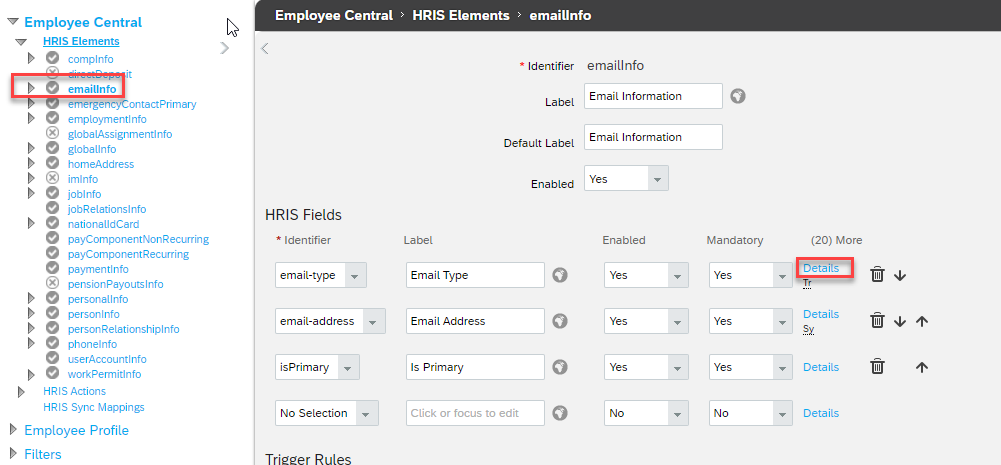
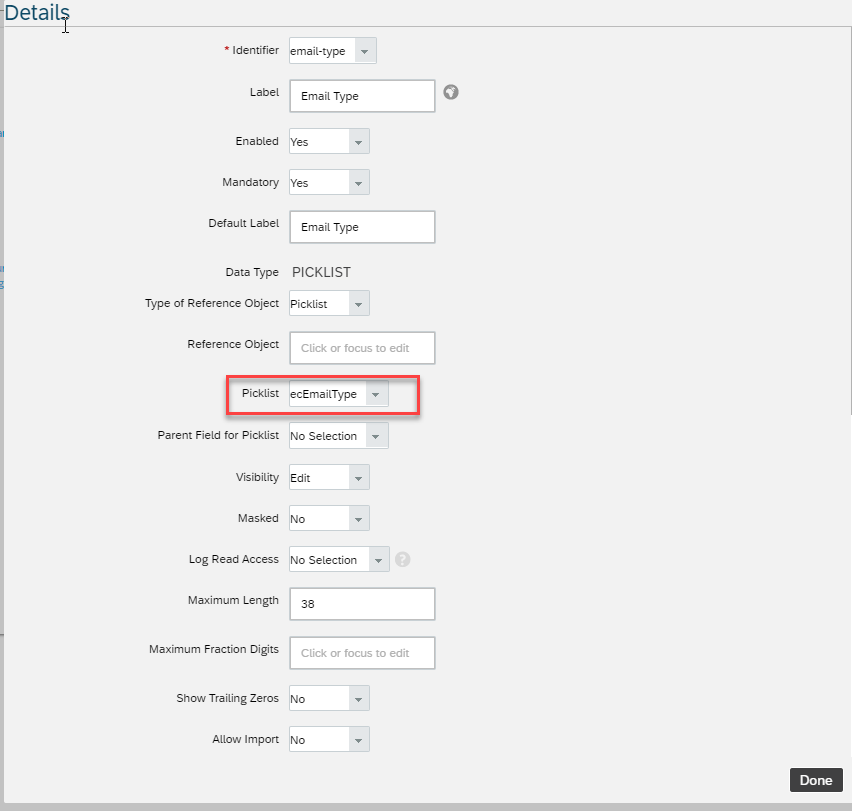
1.3 On the email-type details page, note down the name of the picklist associated with this field. By default, it is ecEmailType. However it may be different in your tenant.
Step 2: Retrieve constant value for emailType
2.1 In SuccessFactors Admin Center, search and open Picklist Center.

2.2 Use the name of the email picklist captured from the previous section (e.g. ecEmailType) to find the email picklist.
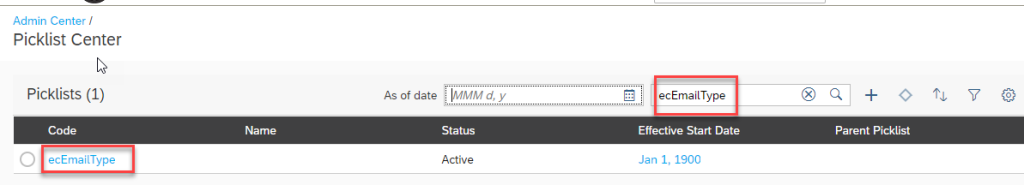
2.3 Open the active email picklist.
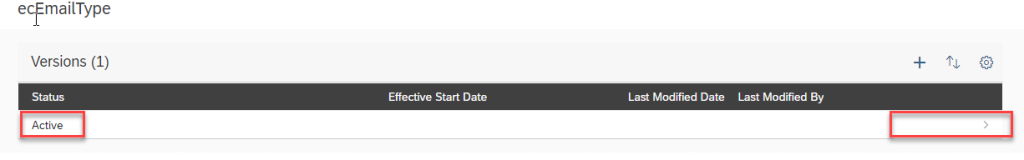
2.4 On the email type picklist page, select the Business email type.
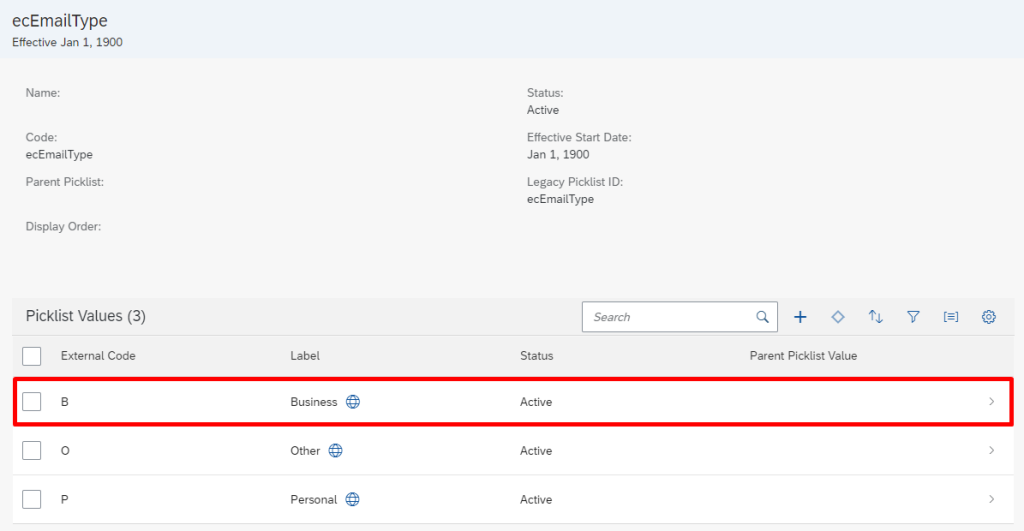
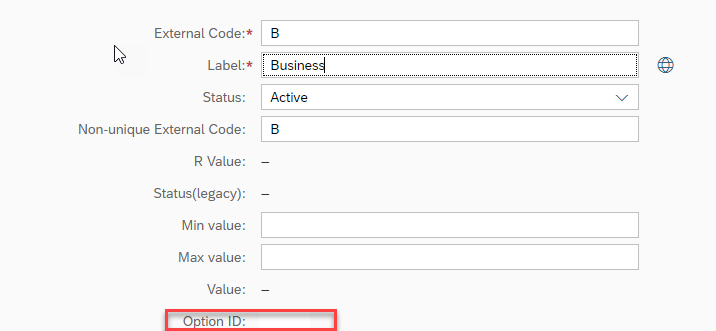
2.5 Note down the Option ID associated with the Business email. This is the code that we will use with emailType in the attribute-mapping table.
Steps need to perform in Microsoft Azure AD
Step 3: Add the provisioning connector app and configure connectivity to SuccessFactors
To configure SuccessFactors Writeback:
3.1 Login to Azure Portal
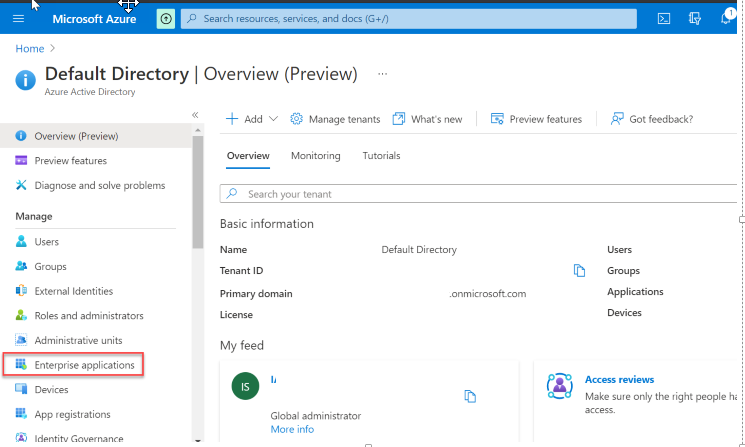
3.2 In the left navigation bar, select Azure Active Directory
3.3 Select Enterprise Applications
3.4 Select All Applications and Select Add an application.
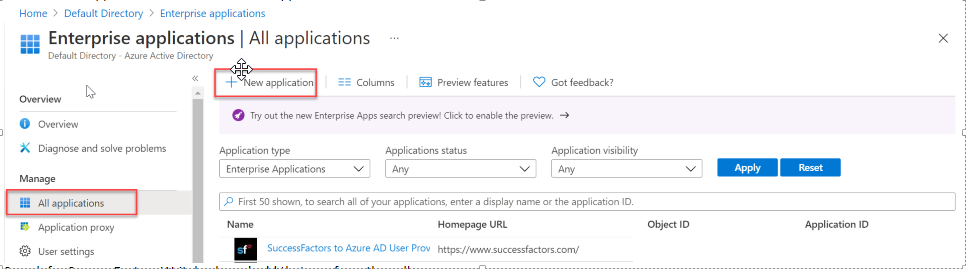
3.5 Search for “SuccessFactors Writeback” and select
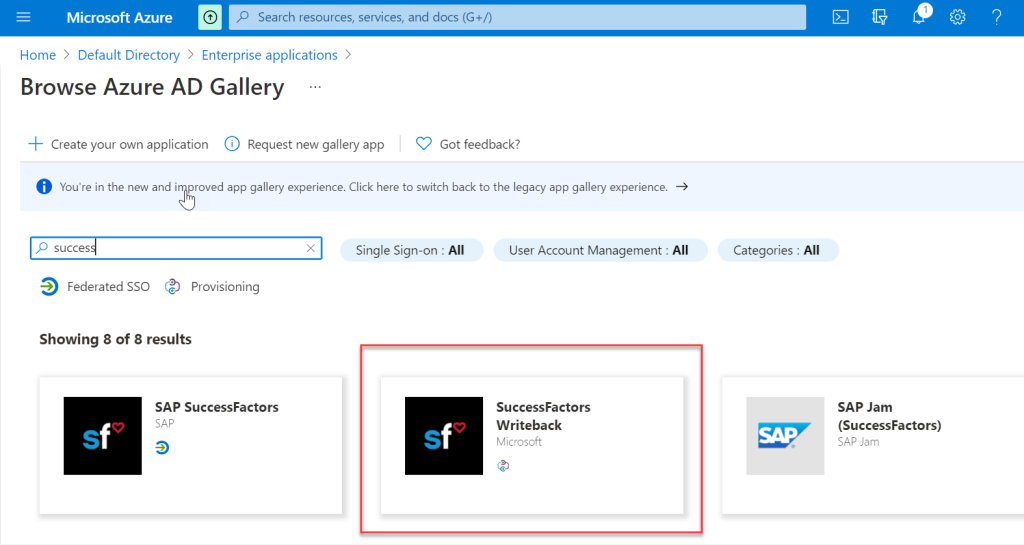
3.6 Click on create and add that app from the gallery.
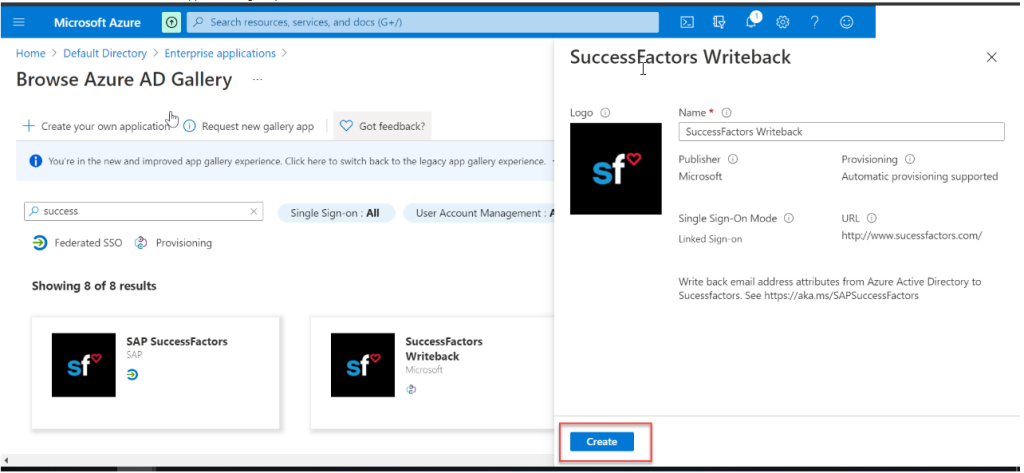
3.7 Wait till adding the application “SuccessFactors Writeback “
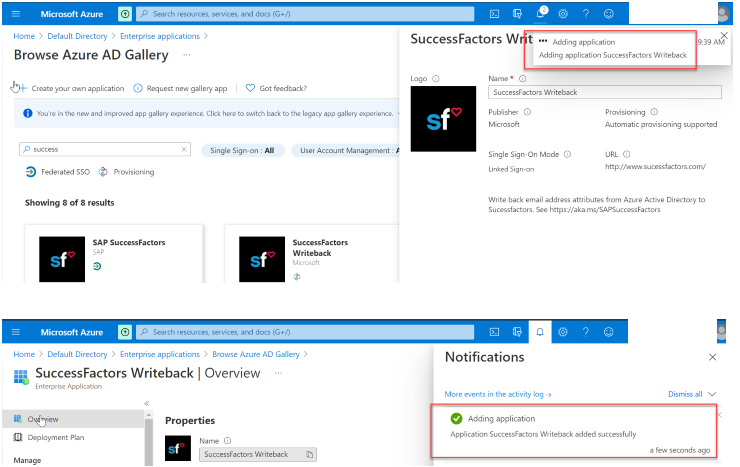
3.8 After the app is added and the app details screen is shown, select Provisioning
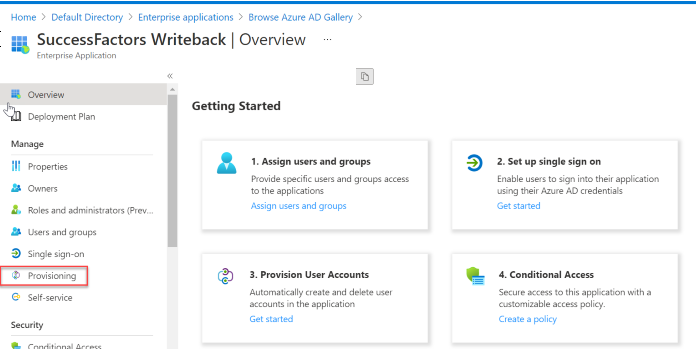
3.9 Click on “Get Started “
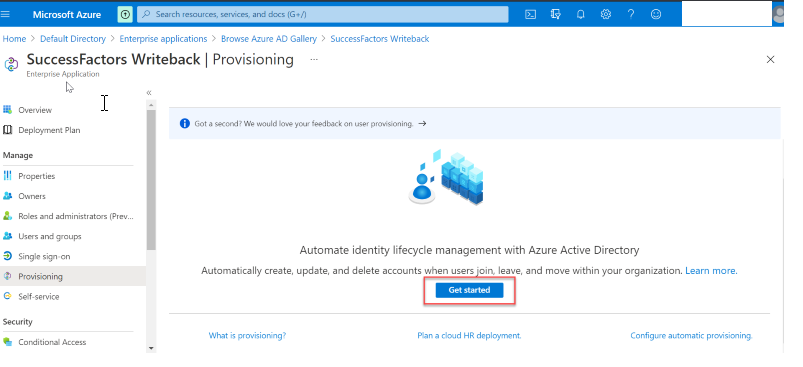
3.10 Change the Provisioning Mode to Automatic
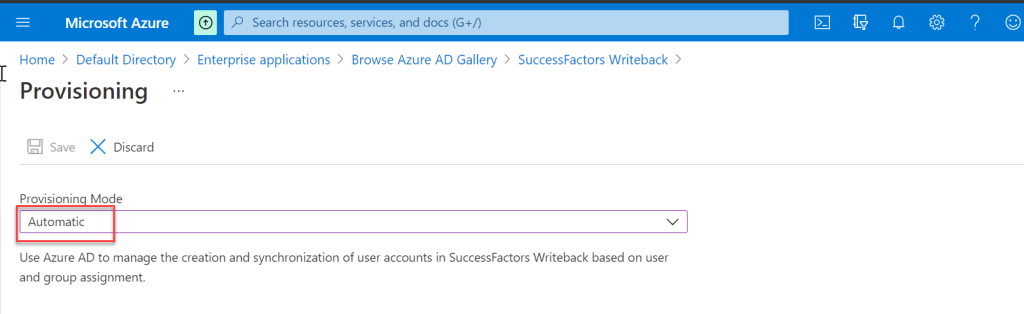
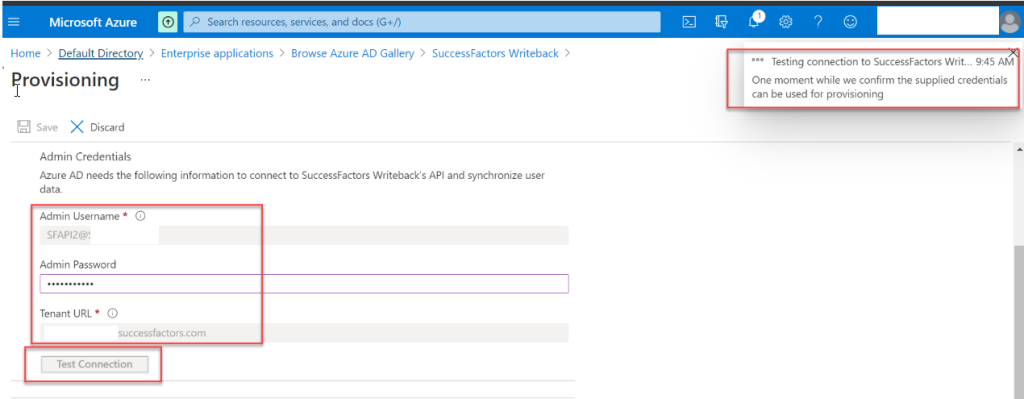
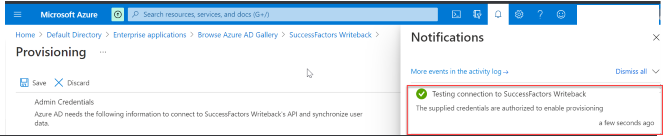
3.11 Complete the Admin Credentials section as below and test the connection.
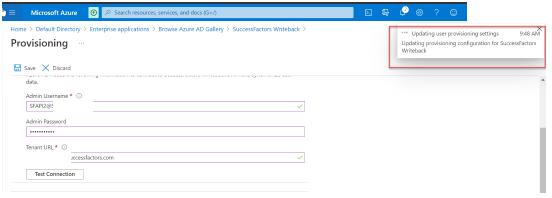
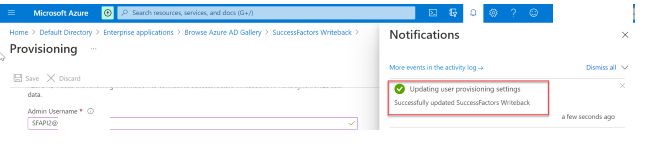
3.12 If the connection test succeeds, click the Save button at the top.
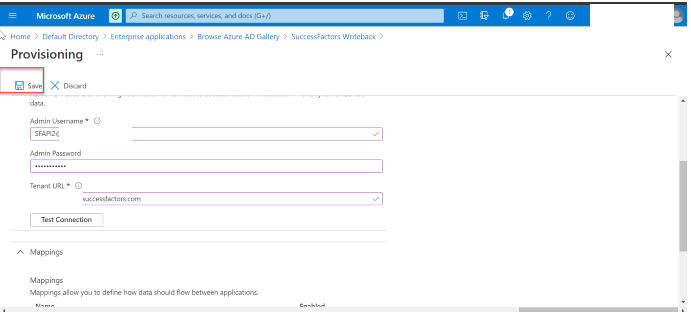
3.13 Once the credentials are saved successfully, the Mappings section will display the default mapping. Refresh the page, if the attribute mappings are not visible.
Step 4: Configure attribute mappings
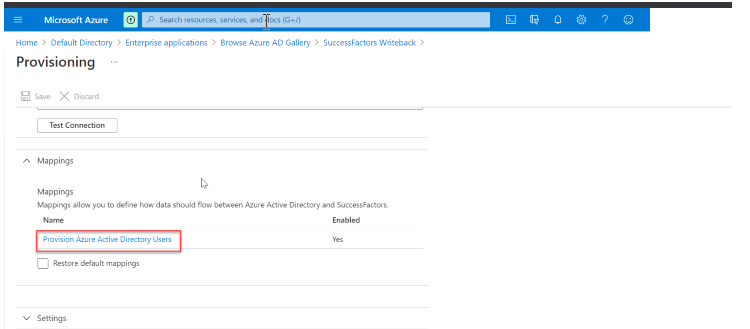
4.1 On the Provisioning tab under Mappings, click Provision Azure Active Directory Users.
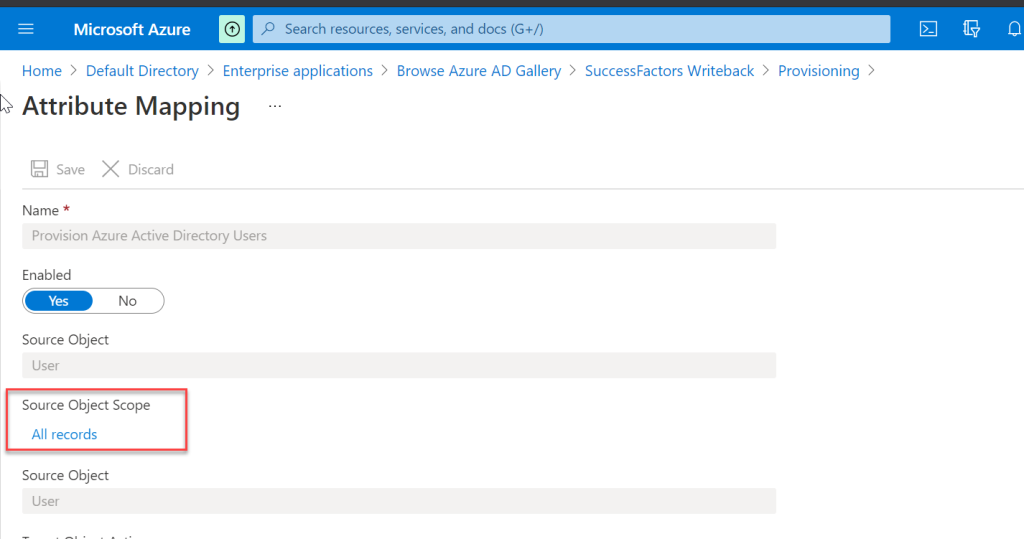
4.2 In the Source Object Scope field, you can select which sets of users in Azure AD should be considered for write-back, by defining a set of attribute-based filters. The default scope is “all users in Azure AD”.
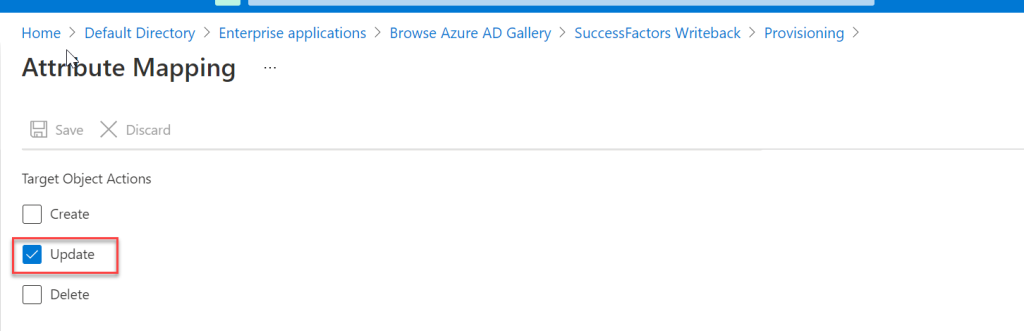
4.3 The Target Object Actions field only supports the Update operation.
4.4 In the mapping table under Attribute mappings section, we can map the following Azure Active Directory attributes to SuccessFactors. The table below provides guidance on how to map the write-back attributes.
Note: I have selected only email for the update in Azure AD -> SuccessFactors and if you have any other requirement like employeeID or mobile number perform the changes accordingly.
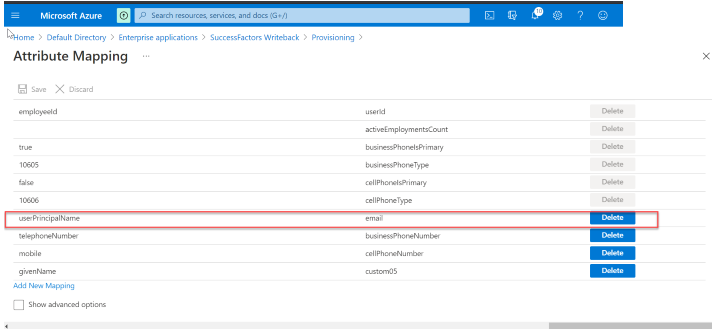
4.5 Validate and review your attribute mappings.
4.6 Click Save to save the mappings.
Step 5: Enable and launch user provisioning
5.1 In the Provisioning tab, set the Provisioning Status to On.
5.2 Select Scope. You can select from one of the following options:
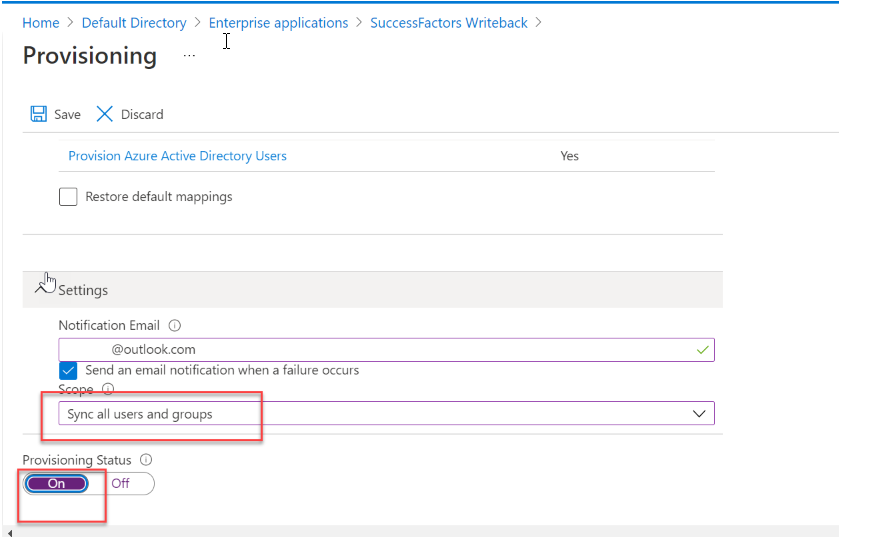
Option 1: Sync all users and groups: Select this option if you plan to write back mapped attributes of all users from Azure AD to SuccessFactors, subject to the scoping rules defined under Mappings -> Source Object Scope.
Option 2: Sync only assigned users and groups: Select this option if you plan to write back mapped attributes of only users that you have assigned to this application in the Application -> Manage -> Users and groups menu option. These users are also subject to the scoping rules defined under Mappings -> Source Object Scope.
Note: I have selected the option 1 so all users will get synced.
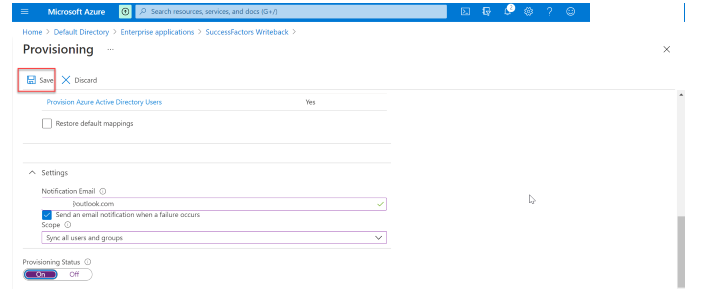
5.3 Click Save.
5.4 This operation will start the initial sync, which can take a variable number of hours depending on how many users are in the Azure AD tenant and the scope defined for the operation. You can check the progress bar to the track the progress of the sync cycle.
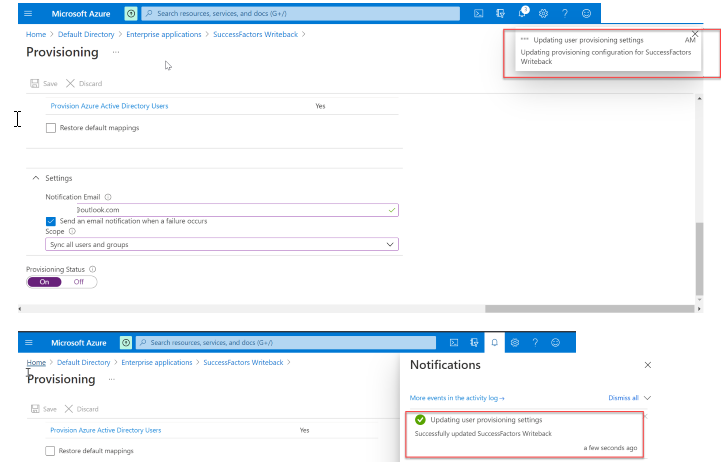
5.5 At any time, check the Provisioning logs tab in the Azure portal to see what actions the provisioning service has performed. The provisioning logs lists all individual sync events performed by the provisioning service.
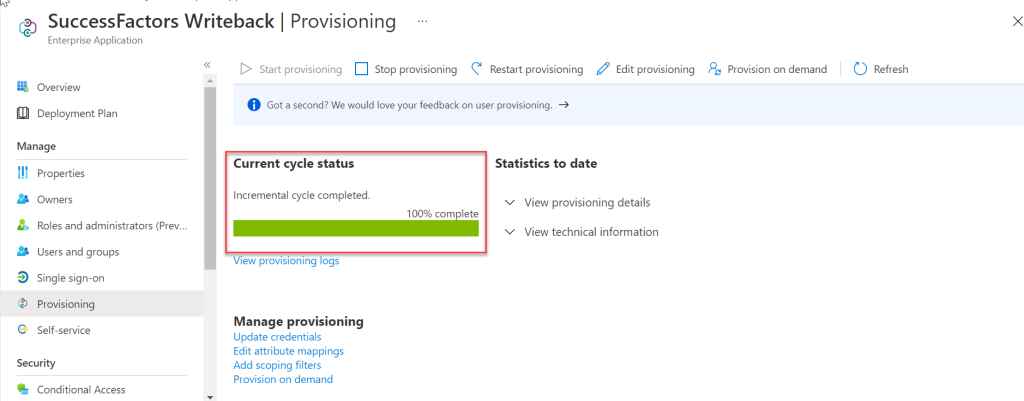
5.6 Once the initial sync is completed, it will write an audit summary report in the Provisioning tab, as shown below.